Breaking Down the Security Intel of a Casino Heist
In the world of high-stakes crime, few operations are as complex and daring as a casino heist. The glamour of the casino environment, combined with the extensive security measures in place, creates a unique challenge for thieves. This case study explores the meticulous planning and intelligence gathering required to execute a successful casino heist, focusing on the critical aspect of obtaining security intel.
The first step in the planning process is reconnaissance. This involves gathering information about the target casino, including its layout, security systems, and employee routines. Thieves often employ a variety of methods for this, including direct observation, social engineering, and even insider information. Observing the casino from a distance allows potential thieves to note peak hours, staff movements, and security patrol patterns. This phase is crucial as it sets the foundation for the entire operation.
Next, thieves may utilize social engineering tactics to extract information from unsuspecting employees. This could involve posing as a maintenance worker, a vendor, or even a patron. By building rapport with staff members, they can gain insights into the casino’s security protocols and weaknesses. This method is particularly effective in environments where employees may not be trained to recognize potential threats. Through casual conversations or even flattery, thieves can gather valuable intel about security measures, such as camera placements, alarm systems, and response times.
In some cases, criminals might recruit insiders who work at the casino. These insiders can provide first-hand knowledge about the inner workings of the security system. They might have access to restricted areas or be familiar with the timing of security shifts. This insider knowledge can be invaluable, as it allows thieves to bypass certain security measures or exploit vulnerabilities that an outside observer would not notice.
Technological tools also play a significant role in gathering security intel. Thieves may use drones to capture aerial footage of the casino, providing a comprehensive view of the layout and security features. Additionally, they might employ hacking techniques to access the casino’s surveillance systems, allowing them to monitor security feeds and identify blind spots. Cybersecurity breaches can reveal critical information about alarm systems and response protocols, further aiding in the planning process.
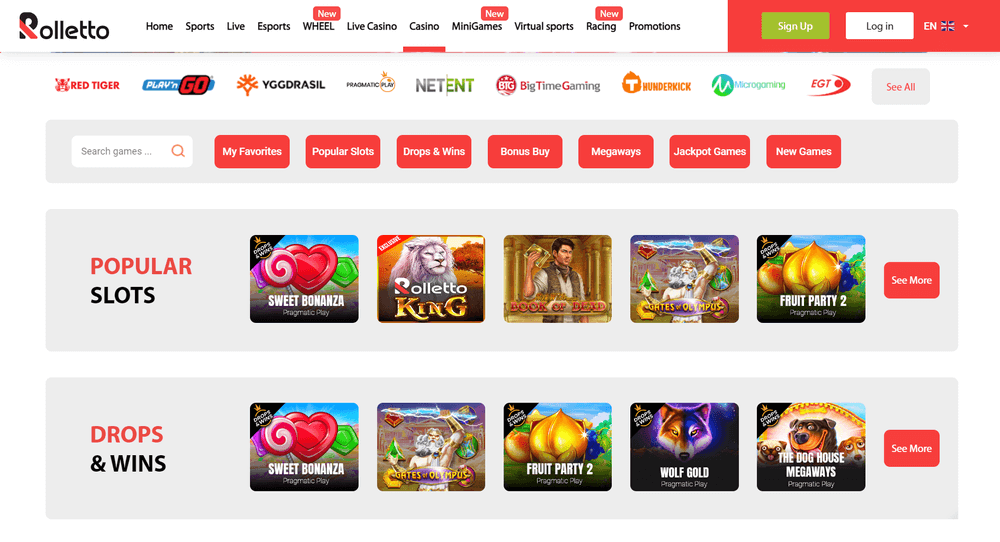
Once sufficient intel is gathered, rolettocasinouk.com the planning phase transitions into execution. The heist is typically conducted during off-peak hours when security personnel are less vigilant. By this point, the thieves have already identified the best routes for entry and exit, the timing of security patrols, and the locations of high-value targets within the casino. This meticulous preparation significantly increases the likelihood of a successful heist.
In conclusion, obtaining security intel for a casino heist involves a combination of reconnaissance, social engineering, insider recruitment, and technological tools. Each element plays a vital role in reducing risk and enhancing the chances of success. While the allure of a casino heist may captivate the imagination, it is the careful planning and intelligence gathering that ultimately determines the fate of such operations. The complexity of these undertakings highlights the need for robust security measures in high-stakes environments, as even the most daring plans can falter without comprehensive preparations.
